Configuring Kerberos Authentication for Databases with a Microsoft Windows 2008 R2 Active Directory KDC
This post describes how to configure an Oracle database for Kerberos authentication with Microsoft Windows 2008 R2 Active Directory, and how to configure the Oracle clients.
Topology
Kerberos Server (Microsoft KDC):
- Host name: addemo1.ziontech.demo
- Microsoft Windows Server 2008 R2 Enterprise Edition with Service Pack 1
- Active Directory (incorporating Kerberos Key Distribution Centre (KDC)
- Realm name: ziontech.demoRealm name: ziontech.demo
Oracle Database:
- Host name: db1.ziontech.demo Host name: db1.ziontech.demo
- Oracle Enterprise Linux 6Oracle Enterprise Linux 6
- Oracle11g R2 Server Enterprise Edition with Oracle Advanced Security Option (ASO) with 11.2.0.4
Oracle Client:
- Host name: win7a.ziontech.demoHost name: win7a.ziontech.demo
- Microsoft Windows 7 64 bitMicrosoft Windows 7 64 bit
- Oracle11g R2 64 bit Client installation with Oracle Advanced Security Option (ASO) with 11.2.0.4
ASO approach in this post works only with Oracle Database and Clients 11.2.0.2 patchset or higher
Section 1: On AD machine
1.1 Create two users (principals in Kerberos terminology)
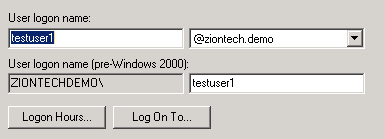
testuser1, which will be used to connect to DB from client
Second for Oracle DB server,
→ Check password never expires option for sever principals
1.2 Create Key Table in Windows 2008 R2
The final step on the Windows 2008 R2 server is to extract a key table for the database server principal. This is done using the KTPASS.EXE tool.
ktpass.exe -princ oracle/db1.ziontech.demo@ZIONTECH.DEMO -mapuser ZIONTECHDEMO\db1.ziontech.demo -crypto all -pass Welcome9 -out c:\keytab
The resulting keytab file should then be transferred to the machine running the Oracle Database
There is a process on how to validate keytab (read this post). Using this approach, we can avoid lot of troubleshooting upfront by ensuring that the KVNO value is compatible.
As mentioned in above referenced post, perform following ldapsearch query to obtain msDS-KeyVersionNumber from Active Directory.
ldapsearch -h ad.ziontech.demo -p 389 -D "testuser1@ziontech.demo" -w "Welcome1" -b "DC=ziontech,DC=demo" -s sub servicePrincipalName=oracle/db1.ziontech.demo msDS-KeyVersionNumber
The output will look like:
CN=db1,CN=Users,DC=ziontech,DC=demo msDS-KeyVersionNumber=6
Then, increment value of msDS-KeyVersionNumber by 1 and pass it as a value to the parameter -kvno in ktpass command.
We can even specify specific supported algorithm(s) for crypto parameter and use this version of ktpass instead of above.
ktpass.exe -princ oracle/db1.ziontech.demo@ZIONTECH.DEMO -mapuser ZIONTECHDEMO\db1.ziontech.demo -crypto AES256-CTS-HMAC-SHA1-96 -pass Welcome9 -ptype KRB5_NT_PRINCIPAL -kvno 7 -out c:\keytab
Section 2: On DB machine
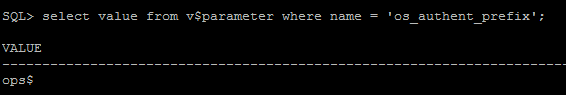
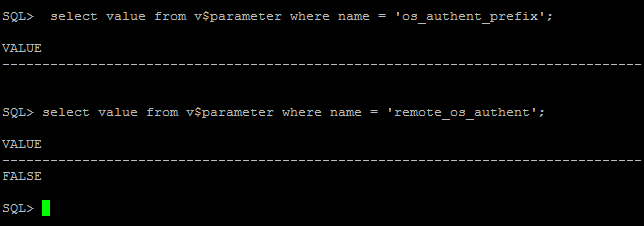
2.1 Verify that the system settings remote_os_authent=false and os_authent_prefix=”” are configured correctly:
SQL> select value from v$parameter where name = 'os_authent_prefix'; SQL> select value from v$parameter where name = 'remote_os_authent';
If you see something like ops$ for os_authent_prefix, it has to be changed to null using following process:
SQL> create pfile='/tmp/pfile.txt' from spfile; SQL> shutdown immediate;
Add this to the “/tmp/pfile.txt” file:
os_authent_prefix=''
Recreate the pfile:
SQL> sqlplus / as sysdba SQL> create spfile from pfile='/tmp/pfile.txt'; SQL> startup
2.2 Configure SQLNET for Kerberos
Modify sqlnet.ora with following configuration:
NAMES.DIRECTORY_PATH= (TNSNAMES, EZCONNECT) ADR_BASE = /app/db1 SQLNET.KERBEROS5_KEYTAB=/app/kerberos/keytab SQLNET.KERBEROS5_CONF=/app/kerberos/krb5.conf SQLNET.KERBEROS5_CONF_MIT=TRUE SQLNET.AUTHENTICATION_KERBEROS5_SERVICE=oracle SQLNET.AUTHENTICATION_SERVICES=(BEQ,KERBEROS5)
Create /app/kerberos/krb5.conf with following content:
[libdefaults]
default_realm = ZIONTECH.DEMO
[realms]
ZIONTECH.DEMO = {
kdc = addemo1.ziontech.demo:88
}
[domain_realm]
.ziontech.demo = ZIONTECH.DEMO
ziontech.demo = ZIONTECH.DEMO
2.3 Create test user on Database
create user "TESTUSER1@ZIONTECH.DEMO" identified externally; grant create session to "TESTUSER1@ZIONTECH.DEMO";
This username must be created in uppercase and must have the realm (Active Directory domain) specified.This username must be created in uppercase and must have the realm (Active Directory domain) specified.
Section 3: On Client Machine
- Login to Windows 7 client as testuser1 to ZIONTECH.DEMO domain
- Since client Windows PC is a member of Active Directory Domain, and the user has logged into the Windows machine as a domain user, user should be able to connect to Oracle Database without need for Oracle client.
- Client is already installed under default location: C:\app\testuser1\product\11.2.0\client_1\
Modify sqlnet.ora to contain following information:
NAMES.DIRECTORY_PATH= (TNSNAMES, EZCONNECT) SQLNET.KERBEROS5_CC_NAME=OSMSFT:// SQLNET.AUTHENTICATION_SERVICES= (beq,kerberos5) SQLNET.KERBEROS5_CONF =c:\kerberos\krb5.conf SQLNET.KERBEROS5_CONF_MIT = true
Create krb5.conf in the location defined above:
SQLNET.KERBEROS5_CC_NAME=c:\kerberos\cc SQLNET.AUTHENTICATION_SERVICES= (beq,kerberos5) SQLNET.KERBEROS5_CONF =c:\kerberos\krb5.conf SQLNET.KERBEROS5_CONF_MIT = true
Create tnsnames.ora
DB1 = (DESCRIPTION = (ADDRESS = (PROTOCOL = TCP)(HOST = db1.ziontech.demo)(PORT = 1521)) (CONNECT_DATA = (SERVER = DEDICATED) (SERVICE_NAME = db1.ziontech.demo) ) )
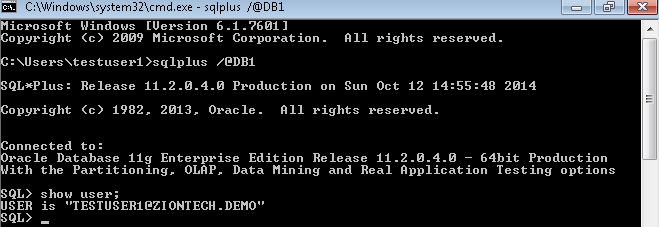
Connect to Database using SQLplus.
User is automatically logged on to database as Oracle Client uses the internal Windows credentials cache.


Leave A Comment